Increasing Concerns On Cloud Services Are Under Attack | Cyber Attack | VARINDIA News Hour

Emotet banking Trojan attack in 2022 | Cyber Security | VARINDIA News Hour
Emotet banking Trojan attack in 2022 | Cyber Security | VARINDIA News Hour
The actor behind Emotet is a hacker group known as Mealybug. Since starting in 2014 with the first and simplest version of the Trojan, they have turned their operation into a successful crimeware rink that provides Malware-as-a-Service (MaaS). The group achieved this by creating a botnet of infected computers on Emotet malware infrastructure, which they then sold access to. The botnet runs from three clusters of servers known as Epoch 1, Epoch 2, and Epoch 3. They rented this framework to various ransomware ventures, including the infamous Ryuk gang. The distribution mechanism of Emotet is through malspam. Emotet ransacks your contacts list and sends itself to your friends, family, coworkers and clients. Since these emails are coming from your hijacked email account, the emails look less like spam and the recipients, feeling safe, are more inclined to click bad URLs and download infected files. If a connected network is present, Emotet spreads using a list of common passwords, guessing its way onto other connected systems in a brute-force attack. If the password to the all-important human resources server is simply “password” then it’s likely Emotet will find its way there.
Emotet continues to be among the most costly and destructive malware affecting SLTT governments. Its worm-like features result in rapidly spreading network-wide infection, which are difficult to combat. Emotet infections have cost SLTT governments up to $1 million per incident to remediate. Emotet malware infiltrates computers through a network spreader component which consists of several spreader modules. The infrastructure that was used by EMOTET involved several hundreds of servers located across the world, all of these having different functionalities in order to manage the computers of the infected victims, to spread to new ones, to serve other criminal groups, and to ultimately make the network morBy VARINDIA| 21 views

The Growing Trickbot Attacks | Trickbot Malware | Posing Concerns | VARINDIA News Hour
The Growing Trickbot Attacks | Trickbot Malware | Posing Concerns | VARINDIA News Hour
TrickBot attack, the Windows services and the activities of Windows Defender or other antivirus software are first terminated. Various methods are then used to extend privileges. The cybercrime operators behind the infamous TrickBot malware have as soon as once more upped the ante by fine-tuning its strategies by including a number of layers of protection to slide previous anti-malware merchandise. The resulting administrative rights can then be used by further plug-ins, which the malware loads automatically. Subsequently, TrickBot spies on both the system and the networks and collects data from the user. The information gathered by the malware is then forwarded to external devices, or to the cybercriminals behind the attack. As per Kaspersky, initially, TrickBot often found its way into the system through phishing emails. This involves sending deceptively genuine fake emails from well-known institutions and companies, which often have an attachment. Victims of a TrickBot attack are requested in the email to open the attachment or link, which leads to the infection of the device. Opening the attachments causes the malware to be downloaded. A TrickBot infection can also occur, through malicious updates or through malware that is already on the end device. Once the malware has made it onto the computer and is able to save the user's data, one of its main goals is to remain undetected for as long as possible.
A Research on Trickbot says, the malware targeting companies in retail, building materials, manufacturing, insurance, and construction with phishing emails are designed to steal credentials. The Trickbot malware is designed to build a botnet—a network of hundreds or sometimes thousands of hacked and connected devices used to launch attacks on organizations and individuals. Russian-based criminals behind the notorious malware known as Trickbot appear to bBy VARINDIA| 24 views

Digital Currency Glitches | Global Concerns | VARINDIA News Hour
Digital Currency Glitches | Global Concerns | VARINDIA News Hour
The ambiguities surrounding the digital currency still leave enough space for the analysis of its unreserved acceptance, trust and anticipation, which are the main drivers for the spread of the network. It is time for the Banks to carefully consider the technology underlying these cryptocurrencies as a potential generic new way of transferring ownership of the value over the long term. Especially Bitcoin is the technology adoption in the presence of network externalities. The growth in digital currencies could make cross-border payments more efficient and help address the $1.7 trillion global trade financing gap. These burgeoning currencies may not solve all trade issues, however, and could further complicate the supply and demand of foreign exchange, especially for countries with limited existing international trade. There is no doubt that the digital currencies are growing: the market is valued at more than $2 trillion and involves more than 15,000 varieties. Based on the Atlantic Council’s CBDC tracker, nine countries or currency unions have launched their digital currencies, while 15 are in the pilot phase. Additionally, 16, including India, are in the development stage, and 40 are in the research stage. Seven are inactive and two have cancelled any plans to launch it.
Digital currencies could provide alternative credit information for trade finance and there’s a $1.7 trillion global trade financing gap, which heavily impacts SMEs who typically don’t have established financial records with banks. Public ledgers of digital currencies could be used to share payment and financial history to underwrite loans for import and export. At the same time, strong privacy protocols would need to be enforced in order to achieve this. The Reserve Bank of India will launch the CBDC from the upcoming financial year. This follows the government’s plans to launch the CBDC that will be backed by blocBy VARINDIA| 17 views

Increasing social engineering attacks - Smishing, vishing, and phishing | VARINDIA News Hour
Increasing social engineering attacks - Smishing, vishing, and phishing | VARINDIA News Hour
We live in a world that’s becoming more digitally dependent. Right from our social interactions to professional interchanges and financial transactions, most take place digitally. Smishing and vishing are two types of fraud that use SMS (smishing) and voice (vishing) to trick people into giving up money or personal information. They’re “social engineering attacks,” meaning that in a smishing or vishing attack, the attacker uses impersonation to exploit the target’s trust. Because 96% of phishing attacks arrive via email, the term “phishing” is sometimes used to refer exclusively to email-based attacks. A recent survey revealed some alarming numbers about Indian companies managing personal identifiable data and electronic health records. While digital resources are enabling, they also leave us vulnerable to cyber criminals as a lot of information regarding our personal and professional lives rests in the digital domain. Cyber insurance or cyber security insurance provides coverage from activities such as identity theft, unauthorized transactions, and more. Buying a cyber insurance policy can safeguard against online frauds. The policy can be bought by anyone who is 18 years and above and can be bought for family members. Nearly 58% of Indian companies have not opted for cyber insurance yet, indicating lack of awareness about cyber-attacks and cyber risk management strategies. The survey by RIMS and JB Boda Group says, as more attacks on utilities and industrial systems emerge, with Ransomware involved, it no longer is an IT related issue, but of the CFO and board.
The COVID-19 pandemic has triggered digital transformation across companies, leading to the creation of a complex IT landscape in the form of public clouds, unfamiliar home networks, external systems connected through APIs, along with a plethora of access points into their sphere of monitoring andBy VARINDIA| 18 views

Increasing cloud complexity leads to cloud repatriation
It is true that increasing #cloudcomplexity can lead to cloud repatriation, which is the process of moving workloads and data from the cloud back to on-premises data centers or other private infrastructure.
Many senior IT leaders struggle with increasing cloud complexity. As organizations adopt more cloud technologies and services, managing and securing their cloud infrastructure can become increasingly challenging. A survey conducted by Dynatrace found that 98% of senior IT leaders reported experiencing cloud-related issues, with 78% of them stating that cloud complexity was their top challenge.
The complexity of cloud environments can arise due to a variety of factors, including multiple cloud service providers, a mix of public and private clouds, and the need to integrate with on-premises infrastructure. This complexity can lead to issues such as security vulnerabilities, data loss, and compliance risks. This will further lead to challenges such as vendor lock-in, data sovereignty concerns, and compliance issues, among others.
Today's Headline in NewsHours
0:00 Intro
2:46 #Twitter to verify the top 10,000 most-followed firms for free
3:17 Italy expresses concern over ChatGPT breaching EU’s GDPR clauses
3:55 #Amazon may get sued for gathering kids' data via Alexa
4:30 Parliamentary panel expresses concern over delay in data protection bill
5:00 Fans complain of Jio Cinema app crashing on IPL opening day
Follow Us On :-
Website:https://varindia.com/
https://www.facebook.com/VARINDIAMagazine/
https://twitter.com/varindiamag
https://www.instagram.com/varindia/
https://www.linkedin.com/company/14636899/admin/
https://in.pinterest.com/varindia/
https://varindia.tumblr.com/
Visit on https://varindia.com/ to know more
Labels & Copyrights :- VARINDIA
#CloudRepatriation, #IncreasedComplexity, #CBy VARINDIA| 24 views

Need to strategize and address the growing | Multi-Cloud Networking Challenges | VARINDIA News Hour
Need to strategize and address the growing | Multi-Cloud Networking Challenges | VARINDIA News Hour
To keep pace with growing user expectations around digital experiences while honouring data privacy and residency regulations, more and more applications are being decomposed and distributed across different cloud platforms. For NetOps and DevOps practitioners, this creates a need for simplifying app-to-app networking across multiple clouds as a foundation for distributing applications. Over 90% of enterprises are embracing a multi-cloud strategy. Simply put, a multi-cloud approach offers significant advantages to organizations seeking to optimize the Three Cs of Cloud: Cost, Capabilities and Compliance. Still, with all the advantages to be gained with a multi-cloud approach, executives should be aware of the downsides. It is time to address multi-cloud networking and distributed cloud services that can seamlessly integrate into your existing infrastructure and provide immediate value-add for existing and new applications to deliver, secure, and interconnect apps in multiple clouds without being an expert in each one by leveraging automation to build app-to-app networking and security policies across multiple clouds. The challenge in multi-cloud adoption is managing complexity, the more cloud environments your organization uses, the more complex the management task becomes. The problem lies in the diversity among cloud vendors. Each public cloud vendor has its own portal, its own APIs, and its own unique processes for managing its environment. Because there is no standardization across public cloud vendors, multiplying vendors means multiplying the management burden.
However, the advantage is from the side of cost control. Multi-cloud is the ability to provide developers and database administrators with a “self-service” experience, that is, the ability to quickly deploy their applications in their cloud environment of choice. Unfortunately, this canBy VARINDIA| 18 views

Safety of CBDC from vulnerability and cyber attacks | CBDC explained | VARINDIA News Hour
Safety of CBDC from vulnerability and cyber attacks | VARINDIA explained | VARINDIA News Hour
#CBDC is a digital form of central bank money that can be accessible to the general public; essentially, it consists of individuals and firms having access to transaction and savings accounts with their home country’s central bank. The Government of India has proposed to issue CBDC, ‘Digital Rupee’ during the FY2022-23 which would be a digital avatar of India’s Fiat Currency, controlled and monitored by the Reserve Bank of India (RBI). CBDC will be a legal tender, being a revamped version of the physical currency, which will eventually reduce cost of currency management. CBDC could help policy-makers achieve goals around payment efficiency, financial inclusion, banking and payment competitiveness, access to safe central bank money in the era of digital payments, and more. People can convert digital currency to physical currency and vice-versa with ease. As per RBI, the digital rupee blockchain being developed by the RBI would be able to trace all transactions, unlike the current system of mobile wallets offered by private companies. The units issued in the digital rupee would be included in the currency in circulation, it added. The RBI's digital currency is likely to debut by early 2023. Currently, the bitcoin blockchain supports up to seven transactions per second and then there are some others that let a few thousand transactions per second. However, security aspects involved in constructing and deploying a central bank digital currency (CBDC).
It is a matter of great concern on the Security part, which is an essential element in the CBDC system. In addition to securing the underlying storage and transfer of value, security involves
aspects of privacy and resilience. Threats must be mitigated to protect the integrity of funds and the confidentiality of users. A secure CBDC system will retain public trust in the central bank. Under an acBy VARINDIA| 22 views

Data Breaching | Cyber Insurance Opportunities | VARINDIA News Hour
Data Breaching | Cyber Insurance Opportunities | VARINDIA News Hour
We live in a world that’s becoming more digitally dependent. Right from our social interactions to professional interchanges and financial transactions, most take place digitally. While digital resources are enabling, they also leave us vulnerable to cyber criminals as a lot of information regarding our personal and professional lives rests in the digital domain. Cyber insurance or cyber security insurance provides coverage from activities such as identity theft, unauthorized transactions, and more with rapidly increasing digitalisation, cyber risks and loss scenarios keep changing quickly. For all risk owners this makes it even more important to learn from past incidents and identify upcoming cybersecurity trends, threats and vulnerabilities. Cyber insurers have already proven that they can be part of the solution when it comes to building up resiliency and preparedness across all industries. The total global economic damage of cybercrime is a controversial issue. Cybersecurity Ventures estimates global economic cybercrime costs to grow by 15% per year over the next five years, reaching $10.5 trillion annually by 2025. In 2021, the number is expected to be $6 trillion up from $3 trillion in 2015. This is no surprise as the cybercriminal world is advancing at a fast pace.
Having cyber insurance is a good idea if the costs make sense — it could be the difference between going out of business and staying afloat. Even if you can afford and qualify for coverage, you should know that cybercriminals like to attack companies with cyber insurance. According to a recent survey, these organizations are over two times more likely to pay ransoms than those without it. Hackers even find out the value of potential victims' coverage by breaking into the insurance companies first so they can demand the highest possible ransom. Once they've extorted organizations with cyber insurance, theBy VARINDIA| 21 views
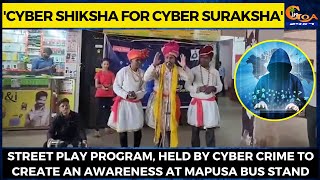
'Cyber Shiksha for Cyber Suraksha' Street play program, held by cyber crime to create an awareness
'Cyber Shiksha for Cyber Suraksha' Street play program, held by cyber crime to create an awareness at Mapusa bus stand
#Goa #GoaNews #streetplay #Cyber #crime #awareness #Mapusa
'Cyber Shiksha for Cyber Suraksha' Street play program, held by cyber crime to create an awarenessBy ingoanews| 26 views
Increasing Concerns On Cloud Services Are Under Attack | Cyber Attack | VARINDIA News Hour
With the new hybrid-working model we see organizations increasingly moving more of their workload settings to the cloud. While this transformation offers great agility and scalability benefits, it comes with inherent and increased risks to security and compliance. A simple configuration error can result in your entire organization being exposed to threat actors who no longer need to break into your data center to access your critical data or conduct ransomware attacks. As per Gartner by 2025, 99% of cloud security issues will be a result of human error when configuring assets and security in the cloud. At a time when organizations are becoming increasingly dependent on third-party cloud vendors such as AWS, Microsoft Azure, IBM and Google Cloud Platform to securely manage their data, concerns around misconfigurations and other vulnerabilities in the cloud are likely to amplify quickly. What’s more, many of the organizations finding themselves at risk have had to accelerate their digital transformation initiatives at an uncomfortable pace over the past two years, resulting in knowledge and talent gaps that only add to their fears around cloud security.
Under the shared responsibility model - a security framework designed to ensure accountability for compromised data and other incidents - the cloud provider will offer basic cloud security, but it's up to businesses themselves to secure their own data within the cloud. To put it in another way, if cloud providers ensure the town gates are locked and the perimeter is well guarded, it’s still up to businesses to ensure their own doors are locked. That’s no mean feat, particularly when you consider that many large enterprises now rely on three or four cloud platforms as part of a multi-cloud strategy. Attacks on cloud service providers are ramping up. As outlined in Check Point 2022 Security Report, the previo
#FACEBOOK#amazon#russia#indianrailways#Microsoft#tutorial#Paypal#AWS#MicrosoftAzure#Varindia#GoogleCloud#Digitalocean#cloudcomputingexplained#OneWeb#ashwanivaishnaw#RailwayMinisterAshwiniVaishnaw#varindianewshour#Cloudsecurity#Azure#hybridworking#CloudServicesUnderAttack#IBMandGoogleCloudPlatform#CSSTricks#GMPCSlicence#Bhartigroup#Instagramban#cloudprovider#whatarecloudservices#typesofcloudcomputingservices#basicofcloudcomputing
Category:
Technology

Emotet banking Trojan attack in 2022 | Cyber Security | VARINDIA News Hour
Emotet banking Trojan attack in 2022 | Cyber Security | VARINDIA News Hour
The actor behind Emotet is a hacker group known as Mealybug. Since starting in 2014 with the first and simplest version of the Trojan, they have turned their operation into a successful crimeware rink that provides Malware-as-a-Service (MaaS). The group achieved this by creating a botnet of infected computers on Emotet malware infrastructure, which they then sold access to. The botnet runs from three clusters of servers known as Epoch 1, Epoch 2, and Epoch 3. They rented this framework to various ransomware ventures, including the infamous Ryuk gang. The distribution mechanism of Emotet is through malspam. Emotet ransacks your contacts list and sends itself to your friends, family, coworkers and clients. Since these emails are coming from your hijacked email account, the emails look less like spam and the recipients, feeling safe, are more inclined to click bad URLs and download infected files. If a connected network is present, Emotet spreads using a list of common passwords, guessing its way onto other connected systems in a brute-force attack. If the password to the all-important human resources server is simply “password” then it’s likely Emotet will find its way there.
Emotet continues to be among the most costly and destructive malware affecting SLTT governments. Its worm-like features result in rapidly spreading network-wide infection, which are difficult to combat. Emotet infections have cost SLTT governments up to $1 million per incident to remediate. Emotet malware infiltrates computers through a network spreader component which consists of several spreader modules. The infrastructure that was used by EMOTET involved several hundreds of servers located across the world, all of these having different functionalities in order to manage the computers of the infected victims, to spread to new ones, to serve other criminal groups, and to ultimately make the network morBy VARINDIA| 21 views

The Growing Trickbot Attacks | Trickbot Malware | Posing Concerns | VARINDIA News Hour
The Growing Trickbot Attacks | Trickbot Malware | Posing Concerns | VARINDIA News Hour
TrickBot attack, the Windows services and the activities of Windows Defender or other antivirus software are first terminated. Various methods are then used to extend privileges. The cybercrime operators behind the infamous TrickBot malware have as soon as once more upped the ante by fine-tuning its strategies by including a number of layers of protection to slide previous anti-malware merchandise. The resulting administrative rights can then be used by further plug-ins, which the malware loads automatically. Subsequently, TrickBot spies on both the system and the networks and collects data from the user. The information gathered by the malware is then forwarded to external devices, or to the cybercriminals behind the attack. As per Kaspersky, initially, TrickBot often found its way into the system through phishing emails. This involves sending deceptively genuine fake emails from well-known institutions and companies, which often have an attachment. Victims of a TrickBot attack are requested in the email to open the attachment or link, which leads to the infection of the device. Opening the attachments causes the malware to be downloaded. A TrickBot infection can also occur, through malicious updates or through malware that is already on the end device. Once the malware has made it onto the computer and is able to save the user's data, one of its main goals is to remain undetected for as long as possible.
A Research on Trickbot says, the malware targeting companies in retail, building materials, manufacturing, insurance, and construction with phishing emails are designed to steal credentials. The Trickbot malware is designed to build a botnet—a network of hundreds or sometimes thousands of hacked and connected devices used to launch attacks on organizations and individuals. Russian-based criminals behind the notorious malware known as Trickbot appear to bBy VARINDIA| 24 views

Digital Currency Glitches | Global Concerns | VARINDIA News Hour
Digital Currency Glitches | Global Concerns | VARINDIA News Hour
The ambiguities surrounding the digital currency still leave enough space for the analysis of its unreserved acceptance, trust and anticipation, which are the main drivers for the spread of the network. It is time for the Banks to carefully consider the technology underlying these cryptocurrencies as a potential generic new way of transferring ownership of the value over the long term. Especially Bitcoin is the technology adoption in the presence of network externalities. The growth in digital currencies could make cross-border payments more efficient and help address the $1.7 trillion global trade financing gap. These burgeoning currencies may not solve all trade issues, however, and could further complicate the supply and demand of foreign exchange, especially for countries with limited existing international trade. There is no doubt that the digital currencies are growing: the market is valued at more than $2 trillion and involves more than 15,000 varieties. Based on the Atlantic Council’s CBDC tracker, nine countries or currency unions have launched their digital currencies, while 15 are in the pilot phase. Additionally, 16, including India, are in the development stage, and 40 are in the research stage. Seven are inactive and two have cancelled any plans to launch it.
Digital currencies could provide alternative credit information for trade finance and there’s a $1.7 trillion global trade financing gap, which heavily impacts SMEs who typically don’t have established financial records with banks. Public ledgers of digital currencies could be used to share payment and financial history to underwrite loans for import and export. At the same time, strong privacy protocols would need to be enforced in order to achieve this. The Reserve Bank of India will launch the CBDC from the upcoming financial year. This follows the government’s plans to launch the CBDC that will be backed by blocBy VARINDIA| 17 views

Increasing social engineering attacks - Smishing, vishing, and phishing | VARINDIA News Hour
Increasing social engineering attacks - Smishing, vishing, and phishing | VARINDIA News Hour
We live in a world that’s becoming more digitally dependent. Right from our social interactions to professional interchanges and financial transactions, most take place digitally. Smishing and vishing are two types of fraud that use SMS (smishing) and voice (vishing) to trick people into giving up money or personal information. They’re “social engineering attacks,” meaning that in a smishing or vishing attack, the attacker uses impersonation to exploit the target’s trust. Because 96% of phishing attacks arrive via email, the term “phishing” is sometimes used to refer exclusively to email-based attacks. A recent survey revealed some alarming numbers about Indian companies managing personal identifiable data and electronic health records. While digital resources are enabling, they also leave us vulnerable to cyber criminals as a lot of information regarding our personal and professional lives rests in the digital domain. Cyber insurance or cyber security insurance provides coverage from activities such as identity theft, unauthorized transactions, and more. Buying a cyber insurance policy can safeguard against online frauds. The policy can be bought by anyone who is 18 years and above and can be bought for family members. Nearly 58% of Indian companies have not opted for cyber insurance yet, indicating lack of awareness about cyber-attacks and cyber risk management strategies. The survey by RIMS and JB Boda Group says, as more attacks on utilities and industrial systems emerge, with Ransomware involved, it no longer is an IT related issue, but of the CFO and board.
The COVID-19 pandemic has triggered digital transformation across companies, leading to the creation of a complex IT landscape in the form of public clouds, unfamiliar home networks, external systems connected through APIs, along with a plethora of access points into their sphere of monitoring andBy VARINDIA| 18 views

Increasing cloud complexity leads to cloud repatriation
It is true that increasing #cloudcomplexity can lead to cloud repatriation, which is the process of moving workloads and data from the cloud back to on-premises data centers or other private infrastructure.
Many senior IT leaders struggle with increasing cloud complexity. As organizations adopt more cloud technologies and services, managing and securing their cloud infrastructure can become increasingly challenging. A survey conducted by Dynatrace found that 98% of senior IT leaders reported experiencing cloud-related issues, with 78% of them stating that cloud complexity was their top challenge.
The complexity of cloud environments can arise due to a variety of factors, including multiple cloud service providers, a mix of public and private clouds, and the need to integrate with on-premises infrastructure. This complexity can lead to issues such as security vulnerabilities, data loss, and compliance risks. This will further lead to challenges such as vendor lock-in, data sovereignty concerns, and compliance issues, among others.
Today's Headline in NewsHours
0:00 Intro
2:46 #Twitter to verify the top 10,000 most-followed firms for free
3:17 Italy expresses concern over ChatGPT breaching EU’s GDPR clauses
3:55 #Amazon may get sued for gathering kids' data via Alexa
4:30 Parliamentary panel expresses concern over delay in data protection bill
5:00 Fans complain of Jio Cinema app crashing on IPL opening day
Follow Us On :-
Website:https://varindia.com/
https://www.facebook.com/VARINDIAMagazine/
https://twitter.com/varindiamag
https://www.instagram.com/varindia/
https://www.linkedin.com/company/14636899/admin/
https://in.pinterest.com/varindia/
https://varindia.tumblr.com/
Visit on https://varindia.com/ to know more
Labels & Copyrights :- VARINDIA
#CloudRepatriation, #IncreasedComplexity, #CBy VARINDIA| 24 views

Need to strategize and address the growing | Multi-Cloud Networking Challenges | VARINDIA News Hour
Need to strategize and address the growing | Multi-Cloud Networking Challenges | VARINDIA News Hour
To keep pace with growing user expectations around digital experiences while honouring data privacy and residency regulations, more and more applications are being decomposed and distributed across different cloud platforms. For NetOps and DevOps practitioners, this creates a need for simplifying app-to-app networking across multiple clouds as a foundation for distributing applications. Over 90% of enterprises are embracing a multi-cloud strategy. Simply put, a multi-cloud approach offers significant advantages to organizations seeking to optimize the Three Cs of Cloud: Cost, Capabilities and Compliance. Still, with all the advantages to be gained with a multi-cloud approach, executives should be aware of the downsides. It is time to address multi-cloud networking and distributed cloud services that can seamlessly integrate into your existing infrastructure and provide immediate value-add for existing and new applications to deliver, secure, and interconnect apps in multiple clouds without being an expert in each one by leveraging automation to build app-to-app networking and security policies across multiple clouds. The challenge in multi-cloud adoption is managing complexity, the more cloud environments your organization uses, the more complex the management task becomes. The problem lies in the diversity among cloud vendors. Each public cloud vendor has its own portal, its own APIs, and its own unique processes for managing its environment. Because there is no standardization across public cloud vendors, multiplying vendors means multiplying the management burden.
However, the advantage is from the side of cost control. Multi-cloud is the ability to provide developers and database administrators with a “self-service” experience, that is, the ability to quickly deploy their applications in their cloud environment of choice. Unfortunately, this canBy VARINDIA| 18 views

Safety of CBDC from vulnerability and cyber attacks | CBDC explained | VARINDIA News Hour
Safety of CBDC from vulnerability and cyber attacks | VARINDIA explained | VARINDIA News Hour
#CBDC is a digital form of central bank money that can be accessible to the general public; essentially, it consists of individuals and firms having access to transaction and savings accounts with their home country’s central bank. The Government of India has proposed to issue CBDC, ‘Digital Rupee’ during the FY2022-23 which would be a digital avatar of India’s Fiat Currency, controlled and monitored by the Reserve Bank of India (RBI). CBDC will be a legal tender, being a revamped version of the physical currency, which will eventually reduce cost of currency management. CBDC could help policy-makers achieve goals around payment efficiency, financial inclusion, banking and payment competitiveness, access to safe central bank money in the era of digital payments, and more. People can convert digital currency to physical currency and vice-versa with ease. As per RBI, the digital rupee blockchain being developed by the RBI would be able to trace all transactions, unlike the current system of mobile wallets offered by private companies. The units issued in the digital rupee would be included in the currency in circulation, it added. The RBI's digital currency is likely to debut by early 2023. Currently, the bitcoin blockchain supports up to seven transactions per second and then there are some others that let a few thousand transactions per second. However, security aspects involved in constructing and deploying a central bank digital currency (CBDC).
It is a matter of great concern on the Security part, which is an essential element in the CBDC system. In addition to securing the underlying storage and transfer of value, security involves
aspects of privacy and resilience. Threats must be mitigated to protect the integrity of funds and the confidentiality of users. A secure CBDC system will retain public trust in the central bank. Under an acBy VARINDIA| 22 views

Data Breaching | Cyber Insurance Opportunities | VARINDIA News Hour
Data Breaching | Cyber Insurance Opportunities | VARINDIA News Hour
We live in a world that’s becoming more digitally dependent. Right from our social interactions to professional interchanges and financial transactions, most take place digitally. While digital resources are enabling, they also leave us vulnerable to cyber criminals as a lot of information regarding our personal and professional lives rests in the digital domain. Cyber insurance or cyber security insurance provides coverage from activities such as identity theft, unauthorized transactions, and more with rapidly increasing digitalisation, cyber risks and loss scenarios keep changing quickly. For all risk owners this makes it even more important to learn from past incidents and identify upcoming cybersecurity trends, threats and vulnerabilities. Cyber insurers have already proven that they can be part of the solution when it comes to building up resiliency and preparedness across all industries. The total global economic damage of cybercrime is a controversial issue. Cybersecurity Ventures estimates global economic cybercrime costs to grow by 15% per year over the next five years, reaching $10.5 trillion annually by 2025. In 2021, the number is expected to be $6 trillion up from $3 trillion in 2015. This is no surprise as the cybercriminal world is advancing at a fast pace.
Having cyber insurance is a good idea if the costs make sense — it could be the difference between going out of business and staying afloat. Even if you can afford and qualify for coverage, you should know that cybercriminals like to attack companies with cyber insurance. According to a recent survey, these organizations are over two times more likely to pay ransoms than those without it. Hackers even find out the value of potential victims' coverage by breaking into the insurance companies first so they can demand the highest possible ransom. Once they've extorted organizations with cyber insurance, theBy VARINDIA| 21 views

'Cyber Shiksha for Cyber Suraksha' Street play program, held by cyber crime to create an awareness
'Cyber Shiksha for Cyber Suraksha' Street play program, held by cyber crime to create an awareness at Mapusa bus stand
#Goa #GoaNews #streetplay #Cyber #crime #awareness #Mapusa
'Cyber Shiksha for Cyber Suraksha' Street play program, held by cyber crime to create an awarenessBy ingoanews| 26 views
VARINDIA

AI is used Towards Client AI Processing
#Artificialintelligence is increasingly being used for client AI processing. This means that AI models are being trained and deployed on client devices, such as smartphones, laptops, and IoT devices. This has a number of advantages, including, Reduced latency, Improved privacy and Reduced bandwidth usage.
Traditionally, AI processing has been conducted by massive clusters of servers in the cloud or data centers. This is because AI models can be very large and complex, and they require a lot of computing power to train and run.
AI is used Towards Client AI ProcessingBy VARINDIA| 256 views

Can Google’s tools combat online misinformation
#Google's efforts to combat misinformation are important because misinformation can have a negative impact on society. It can undermine trust in institutions, lead to violence, and harm democracy. By developing new tools and initiatives, Google is helping to make the internet a safer and more informed place for everyone.
Google has recently unveiled three new tools to combat online misinformation:
· About this Image: This feature, which was initially unveiled earlier in 2023 and is now available globally to English-speaking users through Google Search, provides information about images, including their history, descriptions by users, metadata, and clear indications if an image is generated by AI. Google's AI-generated images are also clearly labelled.
· Fact Check Explorer: This tool allows journalists to verify images by tapping into information from independent organizations.
· AI-generated source descriptions within the Search Generative Experience: This feature provides original sources and insights from reputable publications, which are accessible through the "More About This Page" section in search results.
Can Google’s tools combat online misinformationBy VARINDIA| 172 views

Increasing online Frauds
Recent developments in the technology landscape, including the acceleration of automation, artificial intelligence, and the digitization of industries, are transforming the nature of work. These challenges have immediate and far-reaching implications for India's economy, society, and future prospects.
The Tech Tsunami, characterized by rapid technological advancements, has the potential to drive unprecedented growth and innovation. However, if not harnessed effectively, it could lead to job shrinkage, job displacement and job reduction further leading to increased economic inequality.
Today's Headline in NewsHours
0:00 Intro
3:07 Online gaming firms sent tax notices worth INR 1 lakh cr
3:36 Government plans to introduce regulatory sandbox for OTT apps
4:05 #Microsoft pulling the plug on its metaverse project
4:33 #HMD Global to manufacture own brand of smartphones in India in 2024
5:00 #TechMahindra’s CEO designate Mohit Joshi announces restructuring
Follow Us On :-
Website:https://varindia.com/
https://www.facebook.com/VARINDIAMagazine/
https://twitter.com/varindiamag
https://www.instagram.com/varindia/
https://www.linkedin.com/company/14636899/admin/
https://in.pinterest.com/varindia/
https://varindia.tumblr.com/
Visit on https://varindia.com/ to know more
Labels & Copyrights :- VARINDIA
Increasing online FraudsBy VARINDIA| 181 views
Govt./PSU

IRCTC 11
CRPF signed an MoU with the IRCTC on Railway Reserved e-ticketing system
Watch IRCTC 11 With HD QualityBy CRPF India| 1123452 views

ECI Press Briefing
Press briefing of Election Commission of India on completion of 2nd Phase of #LokSabhaElection2019 and State Legislative Assemblies elections.
#PollingDay #DeskKaMahaTyohaar #NoVoterToBeLeftBehind
Watch ECI Press Briefing With HD QualityBy Election Commission of India| 431662 views

My interview with Jan Man India
Here is my interview with Shri Sudhir Raval on Jan Man India Channel.
Watch My interview with Jan Man India With HD QualityBy Mansukh Mandaviya| 819321 views

Education ???? पर Arvind Kejriwal की जबरदस्त Speech ???? | Latest Motivational Speech | Aam Aadmi Party
Education ???? पर Arvind Kejriwal की जबरदस्त Speech ???? | Latest Motivational Speech | Aam Aadmi Party
#arvindkejriwal #education #aamaadmiparty
Arvind Kejriwal All Interviews:
https://youtube.com/playlist?list=PLiN7YZXz4nOc23gNiOivcdgeYUEpUUqlU
Arvind Kejriwal All Townhalls:
https://youtube.com/playlist?list=PLiN7YZXz4nOdQ-o4kATbxyeNHjD1SyT8n
Arvind Kejriwal in Punjab Series:
https://youtube.com/playlist?list=PLiN7YZXz4nOcJRxl8iqYDKsL26FKUvmSr
Arvind Kejriwal in Goa Series:
https://youtube.com/playlist?list=PLiN7YZXz4nOflmK5x_tdfrryxrSc3SBzm
Arvind Kejriwal In Uttarakhand Series:
https://youtube.com/playlist?list=PLiN7YZXz4nOcZ5TuqFQsJUmwRdNwvKsCT
Arvind Kejriwal on Baba Saheb Ambedkar:
https://youtube.com/playlist?list=PLiN7YZXz4nOfWtKqvMU22KihHk2jiUXdS
Follow Arvind Kejriwal on Social Media :
Follow Arvind Kejriwal on Twitter: https://www.twitter.com/ArvindKejriwal
Follow Arvind Kejriwal on Facebook: https://www.facebook.com/AAPkaArvind/
Follow Aam Aadmi Party on Facebook: https://www.facebook.com/AamAadmiParty
Follow Aam Aadmi Party on Twitter: https://www.twitter.com/AamAamAadmiParty
Education ???? पर Arvind Kejriwal की जबरदस्त Speech ???? | Latest Motivational Speech | Aam Aadmi PartyBy AAP| 209312 views

Blatant Violation of model code of conduct in Odisha
Blatant Violation of model code of conduct in Odisha
Watch Blatant Violation of model code of conduct in Odisha With HD QualityBy Dharmendra Pradhan| 818225 views
Mr Bhupesh Baghel, CM, Chhattisgarh at #FICCIAGM
Mr Bhupesh Baghel, CM, Chhattisgarh in conversation with Dr Jyotsna Suri, Past President, FICCI at #FICCIAGM.
#FICCI #IndianEconomy #Economy #India
Watch Mr Bhupesh Baghel, CM, Chhattisgarh at #FICCIAGM With HD QualityBy FICCI India| 637243 views
Trending Now
Daily Mirror

Nitish Kumar की जगह Jitan Ram Manjhi को CM बनाएंगे BJP ! Mukesh Sahani | Bihar News | #dblive
Nitish Kumar की जगह Jitan Ram Manjhi को CM बनाएंगे BJP ! Mukesh Sahani | Bihar News | #dblive
#HindiNews | #BreakingNews | #Watch | #video |
Get paid membership : https://www.youtube.com/channel/UCBbpLKJLhIbDd_wX4ubU_Cw/join
DB LIVE APP : https://play.google.com/store/apps/details?id=dblive.tv.news.dblivetv.com
DB LIVE TV : http://dblive.tv/
SUBSCRIBE TO OUR CHANNEL: https://www.youtube.com/channel/UCBbpLKJLhIbDd_wX4ubU_Cw
DESHBANDHU : http://www.deshbandhu.co.in/
FACEBOOK : https://www.facebook.com/DBlivenews/
TWITTER : https://twitter.com/dblive15
ENTERTAINMENT LIVE : https://www.youtube.com/channel/UCyX4qQhpz8WQP2Iu7jzHGFQ
Sports Live : https://www.youtube.com/channel/UCHgCkbxlMRgMrjUtvMmBojg
Nitish Kumar की जगह Jitan Ram Manjhi को CM बनाएंगे BJP ! Mukesh Sahani | Bihar News | #dbliveBy DB Live| 0 views

आज आएगा UP का Budget, Budget पेश करने से पहले होगी Yogi Cabinet की Meeting | UP Budget 2024-25
#UPBudget2024 #YogiAdityanath #SureshKumarKhanna
आज आएगा UP का Budget, Budget पेश करने से पहले होगी Yogi Cabinet की Meeting | UP Budget 2024-25
Subscribe to our YouTube channel: https://bit.ly/PunjabKesariTV
Also, Watch ►
Latest News & Updates ► https://bit.ly/PunjabKesariTVLatestNews
Latest News On Jammu & Kashmir ► https://bit.ly/JammuKashmirNews
Delhi News Updates | Punjab Kesari TV ► https://bit.ly/LatestDelhiNewsUpdates
Latest Updates On West Bengal ► https://bit.ly/LatestWestBengalNews
Viral Videos | Punjab Kesari TV ► https://bit.ly/LatestViralVideos
Punjab Kesari National | Latest News & Updates ► https://bit.ly/LatestNationalNews
Exclusive Interviews ► https://bit.ly/PunjabKesariTV-ExclusiveInterviews
Russia Ukraine Crisis Live Updates ► https://bit.ly/UkraineRussiaCrisisUpdates
Latest Updates On International News ► https://bit.ly/LatestInternationalNews
Follow us on Twitter: https://twitter.com/punjabkesari
Like us on FB: https://www.facebook.com/Pkesarionline/
आज आएगा UP का Budget, Budget पेश करने से पहले होगी Yogi Cabinet की Meeting | UP Budget 2024-25By PunjabKesari TV| 0 views

Bikaner News | लोकसभा चुनाव को लेकर कांग्रेस की तैयारी, कार्यकर्ताओ से पार्टी प्रभारी ने की चर्चा
#bikanernews #preparations #loksabhaelections #partyincharge #discussed #latestnews #breakingnews #news
Watch JAN TV on :
Tata Play DTH : 1185
Airtel DTH: 355
JIO Fiber: 1384
https://www.youtube.com/jantvindia/live
Make sure you subscribe to our channel and never miss a new video:
https://www.youtube.com/jantvindia
https://www.facebook.com/jantvindia
https://www.instagram.com/jantvindia/
https://twitter.com/JANTV2012
http://www.jantv.in
Jan TV Live | Hindi News LIVE 24X7 | Jan TV Live | Hindi news 24X7 LIVE
Jan TV | Hindi News Jan TV Live | Jan TV News | Jan TV Live
News Credit -VKJ
Bikaner News | लोकसभा चुनाव को लेकर कांग्रेस की तैयारी, कार्यकर्ताओ से पार्टी प्रभारी ने की चर्चाBy JANTV RAJASTHAN| 0 views

BJP MLA Ganpat Gaikwad ने Eknath Shinde Shiv Sena Leader Mahesh Gaikwad को थाने के अंदर मारी गोलियां
#ganpatgaikwad #maheshgaikwad #eknathshinde
गोलियों की तड़तड़ाहट... भागते... जान बचाते लोग.... बीजेपी नेता की आंखों में खून सवार... ये वीडियो कहीं और का नहीं बल्कि बीजेपी के नेतृत्व में बनी एकनाथ शिंदे सरकार के महाराष्ट्र राज्य का है... गोलियां मारने वाला कोई और नहीं बल्कि मौजूदा विधायक और बीजेपी का प्रतिष्ठित नेता है... सत्ता की हनक ऐसी कि थाने के अंदर गोलियां दाग रहा है...
Subscribe to our YouTube channel: https://bit.ly/PunjabKesariTV
Also, Watch ►
Latest News & Updates ► https://bit.ly/PunjabKesariTVLatestNews
Latest News On Jammu & Kashmir ► https://bit.ly/JammuKashmirNews
Delhi News Updates | Punjab Kesari TV ► https://bit.ly/LatestDelhiNewsUpdates
Latest Updates On West Bengal ► https://bit.ly/LatestWestBengalNews
Viral Videos | Punjab Kesari TV ► https://bit.ly/LatestViralVideos
Punjab Kesari National | Latest News & Updates ► https://bit.ly/LatestNationalNews
Exclusive Interviews ► https://bit.ly/PunjabKesariTV-ExclusiveInterviews
Russia Ukraine Crisis Live Updates ► https://bit.ly/UkraineRussiaCrisisUpdates
Latest Updates On International News ► https://bit.ly/LatestInternationalNews
Follow us on Twitter: https://twitter.com/punjabkesari
Like us on FB: https://www.facebook.com/Pkesarionline/
BJP MLA Ganpat Gaikwad ने Eknath Shinde Shiv Sena Leader Mahesh Gaikwad को थाने के अंदर मारी गोलियांBy PunjabKesari TV| 0 views

Manali Himachal Pradesh | टूरिज्म इंडस्ट्री में खुशी,जन-जीवन अस्त-व्यस्त, मनाली में भारी बर्फवारी
#manali #himachalpradeshnews #tourism #industry #disrupted #heavysnowfall #latestnews #breakingnews #news
Watch JAN TV on :
Tata Play DTH : 1185
Airtel DTH: 355
JIO Fiber: 1384
https://www.youtube.com/jantvindia/live
Make sure you subscribe to our channel and never miss a new video:
https://www.youtube.com/jantvindia
https://www.facebook.com/jantvindia
https://www.instagram.com/jantvindia/
https://twitter.com/JANTV2012
http://www.jantv.in
Jan TV Live | Hindi News LIVE 24X7 | Jan TV Live | Hindi news 24X7 LIVE
Jan TV | Hindi News Jan TV Live | Jan TV News | Jan TV Live
News Credit -VKJ
Manali Himachal Pradesh | टूरिज्म इंडस्ट्री में खुशी,जन-जीवन अस्त-व्यस्त, मनाली में भारी बर्फवारीBy JANTV RAJASTHAN| 0 views